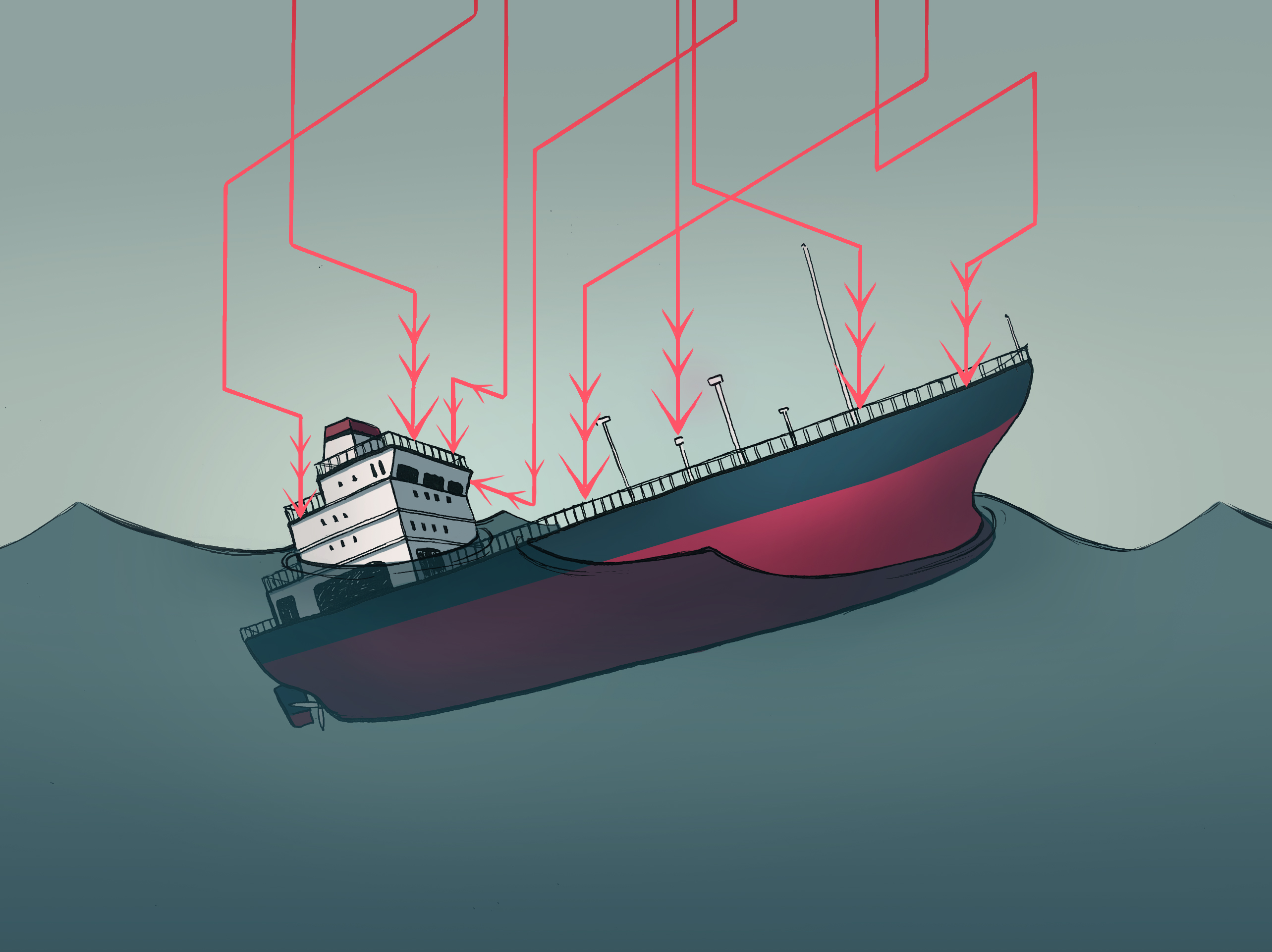
Protecting ships against modern-day pirates
Cybersecurity, long viewed as a secondary concern for naval systems, has become increasingly important in recent years. Ships can no longer be seen as isolated objects at sea, naturally protected from cyber-attacks. Yvon Kermarrec, a researcher in computer science at IMT Atlantique, leads a research chair on cybersecurity in partnership with the French Naval School, Thales and Naval Group. He explains the cyber-risks affecting military and civil ships and the approaches used to prevent them.
[divider style=”normal” top=”20″ bottom=”20″]
This article is part of our series on Cybersecurity: new times, new challenges.
[divider style=”normal” top=”20″ bottom=”20″]
Are ships just as vulnerable to cyber-attacks as other systems?
Yvon Kermarrec: Ships are no longer isolated, even in the middle of the Atlantic Ocean. Commercial boats frequently communicate with ports, the authorities and weather centers, for example. They must remain informed about currents, weather conditions, the position of icebergs etc. They must also inform shipyard owners and ports of arrival when they are running late. For military ships, there is also the communication required for coordinating operations with other naval ships, fighter planes, control centers, etc. This means there are several data streams flowing to and from a given boat. And these streams are just as vulnerable as those connecting an intelligent car with its infrastructure or a computer to its network.
What are the cyber security risks for a boat?
YK: There are many different types of cyber-attack. For example, a military frigate’s combat system software features several millions of lines of code, not to mention the management and control systems for the boat itself, and for its engines and steering in particular. Possible attacks can involve the software pirate altering the digital maps used for navigation or the GPS data, causing the captain to misjudge the boat’s position. This could cause the boat to be lost at sea or run aground by steering it towards a shelf or reef. This is a technique that can be used by pirates who want to take the goods in a container ship. It is also possible to attack the engine controls and perform maneuvers at full speed which would destroy the propulsion system and cause the boat to drift. Finally, we could also imagine someone causing the door of a ferry to open while it is in open water, leading to a major leak and possibly shipwreck.
What do cyber-attacks on boats look like?
YK: They can be generic, meaning that they are generic attacks that impact the boat without specifically targeting it. This could, for example, involve email phishing that lures an employee or tourist on board into opening an email containing a virus. This virus would then spread to the boat’s computer system. There is nothing to prevent ransomware on a boat, which would lock all the computers on board and require a ransom in exchange for unlocking the system. Attacks can also be specific. A criminal can find a way to install spyware on board or convince a systems operator on board to do so. This software would then be able to spy on and control the equipment and transmit sensitive information, such as the boat’s position and actions. The installation of this type of software on a military vessel poses very serious security concerns.
How can all of these attacks be detected?
YK: This is the big challenge we’re facing, and it is what drives part of our research. The goal is to detect anomalies which do not normally occur. We look for early warning signs of attacks. A message that an outer door will open while a ferry is cruising is not normal. To anticipate a door opening, we try to detect the orders that must occur before the action occurs and analyze the context of these actions.
Once the attack has been detected, what strategy is taken?
YK: The first step is to accept that the system will be attacked. Then we must measure the impact to assess the situation and prevent everything from shutting down. This part is called cyber-resiliency: working to ensure that as many functions as possible are maintained to limit the consequences of the attack. If the navigation system is affected, such as the GPS information, the captain must be able to shut down this part of the system and maintain the steering commands. It is certainly inconvenient to operate without the GPS, but there is always the possibility of getting out a map while the navigation system is being restarted or reinstalled. In the case of an action on the external door of a ship out at sea, he will decide to shut down the entire control system for opening the doors. And if it is necessary to open or close other doors, the teams on board can do so manually. It is a tedious procedure, but a much better alternative to dealing with a leak. Research on the subject of detection and action during attacks focuses on finding the necessary means for isolating the various systems and ensuring that the attacks do not spread from one system to another. At the same time, we are also working on defense systems using cryptographic mechanisms. In this case, we are confronted with familiar problems and strategies, similar to those used to protect the Internet of Things.
Ultimately this is all very similar to what is done for communicating cars. But are these problems taken into consideration in the marine setting?
YK: They are beginning to make headway, but for a long time boats were seen as little isolated factories out at sea which were not vulnerable to computer attacks. One of the major challenges is therefore to raise awareness. Sailors often see cybersecurity as a constraint. What they see are the actions they are not able to perform. Yet we all know the limitations of models which ban things without explanation… The sailors and all those involved could potentially be affected both individually and collectively.
What is being done to raise awareness about these issues in the marine setting?
YK: We are addressing this issue in the context of the Chair of Cyber Defense for Naval Systems, which includes the French Naval School and IMT Atlantique. For the Naval School, we developed a cyber-security curriculum for cadet officers. We presented concrete case studies and practical assignments on platforms developed by the Chair’s PhD students. In our discussions with businesses, we now see that ship-owners are taking cyber-risks very seriously. On a global level, the National Cybersecurity Agency of France (ANSSI) and the International Maritime Organization (IMO) are working to address the cybersecurity of ships and port infrastructures. They are therefore responding to the growing concerns in the civil maritime sector. Interest in the subject has greatly increased due to current events and threats that have materialized. Currently, IT security risks for ships are taken very seriously because they could greatly impact international trade and the environment. After all, this maritime context is where the term “pirate” first emerged. There are still considerable challenges and issues at stake for individuals and nations.


Leave a Reply
Want to join the discussion?Feel free to contribute!